Uncompromising Protection with the Highest Level of WordPress Security
Your organization’s most sensitive data stays protected with multi-layered security trusted by banks, pharmaceutical companies, public utilities, and government agencies. Meet even your strictest compliance requirements with the only WordPress platform holding FedRAMPⓇ Authority to Operate (ATO) certification.
Vulnerability management
WordPress VIP addresses one of the biggest challenges in WordPress security: keeping all platform code secure and up-to-date. We help manage necessary components, notify you of vulnerabilities, and respond to and patch issues.
Patch management
We monitor regular security patches for WordPress. Because WordPress VIP is managed by active members of the WordPress community, when an issue arises, we immediately patch it ahead of the fix getting pushed to WordPress core code.
Security testing
We perform regular internal security testing and engage with third parties to perform platform vulnerability assessments.
Penetration testing
We continuously test our infrastructure for vulnerabilities and routinely engage independent third parties to run penetration tests against our platform.
Vulnerability notifications
Customize vulnerability alerts based on notification channel and severity of issues. Integrate notifications into existing emergency response processes via chats, email, webhooks, and more.
Code and plugin scans
We use a bot to scan code, plugins, and themes as part of pull requests created in an application’s GitHub repository. This can help identify potential security concerns before code goes into production.
Logging and auditing
We log activity at the application, web server, load balancer, database, and operating system layers. This allows us to analyze and investigate security issues in real-time.
Anti-spam
We enable you to easily filter out spam from user submitted content using our Akismet anti-spam API.
Controlled changes
Application code is deployed through Kubernetes to Docker containers from version control onto a read-only file system, ensuring changes are only possible via the developer workflow.
Automated core WordPress updates
We alert all customers of upcoming WordPress updates and make sure you are on the latest version of the platform.

Avoiding CMS Disaster: Raising Your WordPress Security to the Next Level
Network security
WordPress VIP provides security throughout your network. From edge security to protection of data in transit between components, WordPress VIP ensures secure communications.
DDoS protection
We have network-wide DDoS protection features to help you get the performance you need. We continuously monitor web traffic and take active mitigation steps when suspicious activity is detected.
Firewalls
Our platform includes network and host-based firewalls with real-time notification processes designed to prevent unauthorized access attempts.
Secure inter-component communication
Using a dynamic environment firewall we ensure the resources for your environments are secured and available only to legitimate network traffic.
Encryption at rest
WordPress VIP provides encryption at rest by default for customer applications and databases for increased protection of confidential information.
“We’re really pleased with WordPress VIP’s commitment to cybersecurity and the way [it] stores [its] data and all the various checks and balances to keep somebody from being able to get access to our site.”
Lead UX Designer, from “The Total Economic Impact™️ of WordPress VIP”
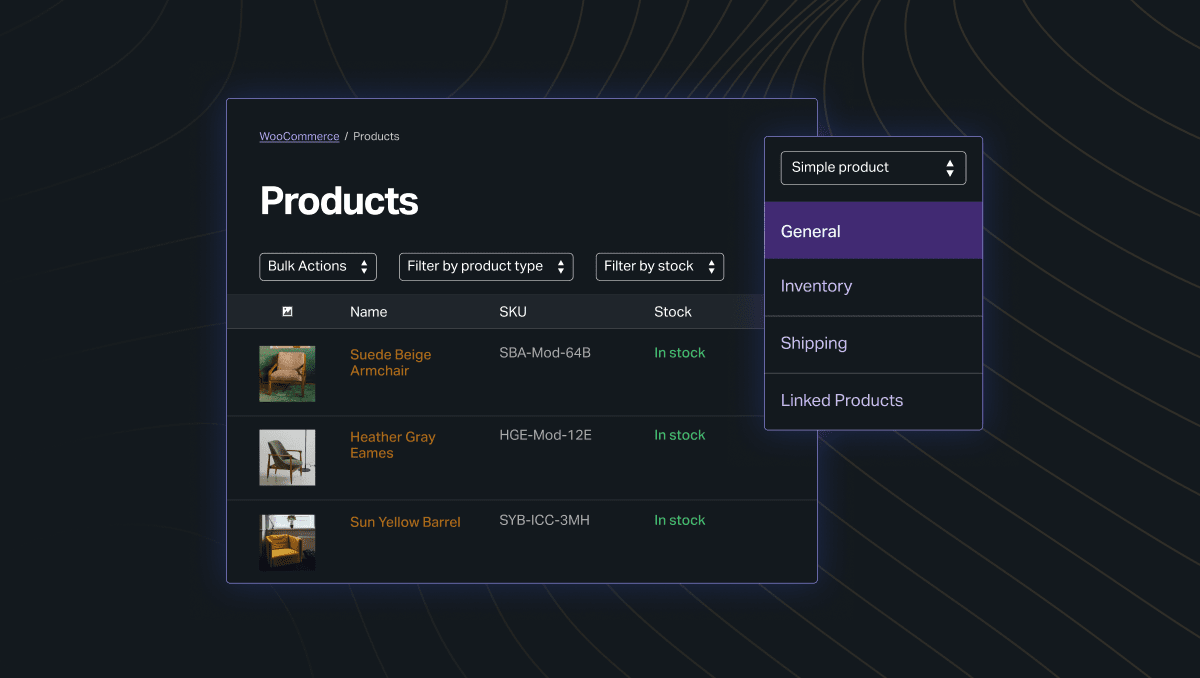
Master Enterprise WordPress Development with VIP Learn
Written by developers for developers, WordPress VIP Learn offers in-depth security, performance, VIP architecture, and tooling courses.
Data protection
With WordPress VIP, every piece of your infrastructure is your own. Using containerization across each piece of the environment, we protect each customer’s data and reduce the risk of attack.
Database security
We maintain separate containerized database infrastructure for every client and application, each with their own unique authentication. This mitigates the risk of unauthorized access between applications.
File system security
We run all web application containers and file systems holding uploaded media in read-only mode. This helps protect applications on the platform against common attacks that allow installation of backdoor shells and other malicious files, delivering the highest level of WordPress security.
Application security
We maintain containerized instances of the WordPress application and Node.js applications, each with processes, memory, and file system. This improves the security of both WordPress and Node.js application environments.
Data center security
Our origin data centers meet the International Organization of Standardization (ISO), International Electrotechnical Commission (IEC) 27001 certification, Standards for Attestation Engagements (SSAE) No. 18 (SOC1) and SOC2 Type 2.
Encrypted backups
Production database backups are taken each hour and maintained for 30 days, stored in an encrypted format to ensure data continuity while maintaining security.
Managed TLS
Our platform automates procurement and renewal of TLS certificates from Let’s Encrypt, ensuring certificates are always valid. Customers may also procure their own certificates from any TLS certificate authority.
Access and authentication
WordPress VIP is built on a robust foundation of granular access controls and permissions.
Access controls
We enable granular access controls to give you the maximum ability to limit permissions and resources to only those employees or contractors that need them.
Multifactor authentication
We fully support multifactor authentication to provide an extra layer of protection in case a password is compromised.
Brute force protection
We automatically detect brute force attacks at the network level, monitoring for unnatural behavior and dynamically applying restrictions.
Customer data access
When we perform operations such as reviewing code or troubleshooting issues, access to customer data is strictly controlled to those employees performing such activities—and internal access is logged for an audit trail.
Physical security
Our data center equipment is housed in dedicated cages to separate our physical infrastructure from other tenants. Access is limited and is subject to ongoing surveillance reviews.

Breach recovery
While WordPress VIP delivers the highest level of WordPress security, in the unlikely event of a breach, we help you quickly recover and get back to business.
Multiple levels of backup
We maintain hourly backups of data both within our origin datacenter and at offsite locations to ensure rapid recovery from any issue.
Disaster recovery procedures
We maintain emergency and contingency plans, including redundant storage and procedures for recovering data. These help reconstruct data in its original or last-replicated state before the moment it was lost.
Security breach procedures
If we discover a security breach involving your site data, we will, except to the extent prohibited by applicable law, notify you of any third-party legal processes received by us relating to the breach, and cooperate with you in investigating and remedying the breach.


