WordPress VIP Blog
Popular Now
-
WordPress VIP Gets Down to Business With the BBC
WordPress VIP CEO Nick Gernert talks WordPress, open source software, and engaging customers at scale Engaging customers in the post-social world with BBC Business Weekly presenter Aaron Heselhurst.
-
NJI Named WordPress VIP Silver Agency Partner
We are proud to welcome NJI as a new agency partner! They are a full-service, global creative agency specializing in policy and public affairs.
-
Collaboration to Support, Discover Why Our Customers Love WordPress VIP
Discover why customers love partnering with WordPress VIP, from strategic planning sessions to reliable applications, user-friendly interfaces, and responsive support.
-
VIP Platform Improvements, New Editorial Capabilities, Streamlined Development and Deployment
Learn what’s new in WordPress VIP, including upgrades to the VIP Dashboard, new editorial capabilities, and streamlined development and deployment.
-
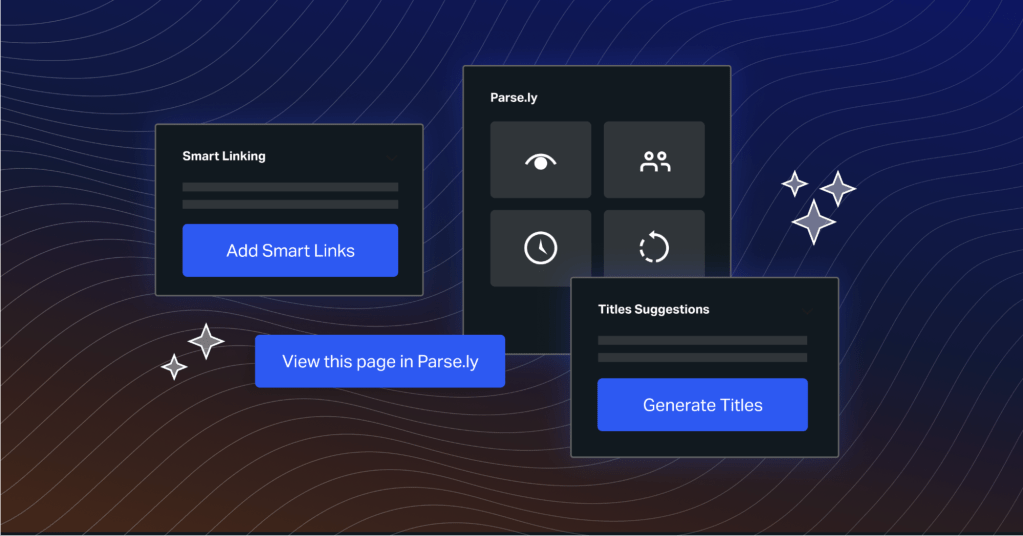
Introducing the Content Helper: From RAG to Riches
We are excited to announce the release of major updates to the Parse.ly Content Helper. Learn more about this new feature here.
-
What’s New in WordPress 6.5 and What Does It Mean for the Enterprise?
Learn what’s new in WordPress 6.5 for enterprise users, including new APIs, improved font management, and usability improvements.
-
WordPress VIP Top Five Technical FAQs
We’ve compiled the top five frequently asked questions on technical aspects of the WordPress VIP platform. Find out what you can integrate, what you can measure, and what you can build with WordPress VIP.
-
Reducing the Burden on IT and Website Administration With VIP
WordPress VIP’s user-friendly dashboard, automatic backups, and robust security features can reduce the burden on IT and website administration, ensuring a stress-free day for web administrators.
-
WordPress VIP and rtCamp Partner to Help Businesses Adapt to New Web Privacy Standards
As the digital landscape undergoes a profound transformation with heightened privacy standards, WordPress VIP and our Gold Agency Partner rtCamp are joining forces to offer a complimentary website audit.
-
IT Monks Named a WordPress VIP Silver Agency Partner
IT Monks is a leading digital agency specializing in custom and optimized website development. With an incredible team boasting over 15 years of industry experience, IT Monks takes on unique WordPress websites of any complexity to create high-performing, visually outstanding solutions.
Request a WordPress VIP demo
Learn how we can help drive business growth for your organization.